As cryptocurrencies continue to gain popularity, securing digital assets is more critical than ever. While online exchanges and software wallets provide convenience, they are susceptible to hacks and phishing attacks. Hardware wallets like Ledger offer enhanced security, and the core of using these wallets is the Ledger Login process. Ledger Login allows users to safely access their wallets and manage crypto assets securely.
This comprehensive guide explores everything you need to know about Ledger Login in 2025, including setup, login procedures, security features, troubleshooting, and best practices.
Ledger Login is the process used to authenticate access to a Ledger hardware wallet using Ledger Live, the official wallet management software. Unlike traditional logins that use usernames and passwords, Ledger Login relies on hardware-based security, PIN verification, optional passphrases, and secure communication between your device and Ledger Live.
One of the key features of Ledger Login is that your private keys never leave the device. All transactions are signed internally, ensuring that your crypto assets remain safe from malware, phishing attacks, and unauthorized access.
Ledger Login provides multiple layers of security to protect your digital assets:
Private keys are stored offline on the Ledger device itself, completely isolated from the internet or connected computers. This makes it extremely difficult for hackers to gain access remotely.
Ledger devices require a secure PIN to unlock. The PIN is entered directly on the device, which randomizes the number layout to prevent keylogger attacks and observation.
Ledger allows users to add an extra passphrase, creating hidden wallets. Even if your device is stolen, these wallets remain inaccessible without the correct passphrase.
The Ledger device verifies firmware authenticity every time it starts. If the firmware has been tampered with, the device will prevent login to protect your funds.
Every transaction or sensitive operation must be physically approved on the Ledger device, ensuring full user control and protection against remote attacks.
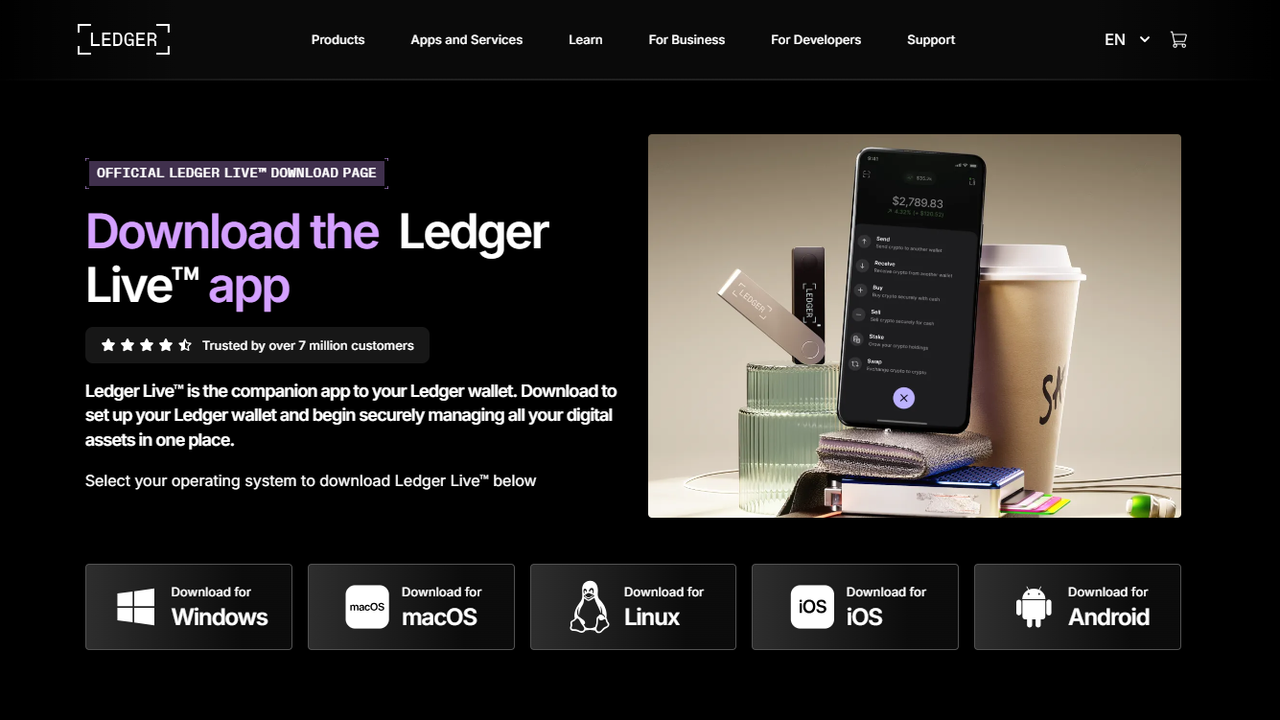
Ledger Login requires Ledger Live, the official companion app. You can download it from https://www.ledger.com/ledger-live for Windows, macOS, or Linux. Desktop apps provide the most secure experience and full features.
Connect your Ledger Nano S, Nano S Plus, or Nano X using the provided USB cable. The Nano X also supports Bluetooth. Ledger Live will detect your device and prompt you to start the login process.
Your Ledger device requires a PIN to unlock. Enter the PIN directly on the device. The device’s number layout is randomized to prevent malicious observation or keylogger attacks.
Once your device is unlocked, Ledger Live displays all your accounts, balances, and transaction history. Ledger Login ensures your private keys never leave the device while allowing you to manage your assets.
During setup, Ledger generates a 24-word recovery phrase. This is the most important backup of your wallet and the only way to restore access if your device is lost, stolen, or damaged.
Important Guidelines:
After logging in, Ledger Live allows you to manage multiple accounts across various cryptocurrencies. Users can:
Always verify addresses on your Ledger device screen to prevent malware or phishing attacks.
Passphrases add an extra layer of security by creating hidden wallets accessible only with the correct passphrase.
Ledger devices check firmware authenticity at startup. Unauthorized firmware will prevent login.
All sensitive transactions are signed offline inside the device, ensuring your private keys never leave the hardware wallet.
Ledger devices are designed to show visible signs of tampering, making physical attacks detectable.
If you forget your PIN, reset the device using your 24-word recovery phrase.
Update Ledger Live to the latest version and ensure your system is compatible.
Always confirm addresses and amounts on the device screen to prevent errors or phishing attacks.
Ledger Login is the foundation of secure cryptocurrency management. With hardware-based key storage, PIN authentication, passphrase protection, and physical confirmation for transactions, Ledger ensures your assets remain secure from hacks, malware, and phishing attacks.
By following these steps and best practices, both beginners and advanced users can confidently manage their crypto portfolios. Ledger Login gives you complete control and peace of mind in securing your digital wealth.